In an environment where every user device serves as a potential laboratory for sophisticated adversaries, the modern mobile application has effectively become a messenger operating deep within enemy territory. Unlike the centralized architecture of the past, today’s mobile ecosystem forces developers to relinquish control the moment a user initiates a download. This shift from protected server-side environments to decentralized, user-controlled hardware has rendered traditional security perimeters obsolete. The industry is currently witnessing a fundamental transition in how digital assets are protected, moving away from simple bug-hunting toward a model of continuous, hardware-backed resilience. As organizations grapple with this new reality, the gap between rapid deployment and data integrity continues to widen, demanding a radical reassessment of what it means to secure a mobile binary.
The transition toward mobile-first operations was once viewed as a mere extension of the web, yet it has fundamentally altered the threat landscape. Organizations now find themselves managing thousands of unique endpoints, each capable of being probed, decompiled, and manipulated by anyone with basic technical curiosity and a set of open-source tools. This lack of physical and environmental control is the defining challenge of modern software engineering. It requires a departure from the “trust but verify” model of the desktop era, favoring instead a model of absolute skepticism toward the execution environment. By acknowledging that the application binary is essentially a public document, development teams can begin to build the necessary layers of defense that survive even when the underlying operating system is compromised.
The Messenger in Enemy Territory: Why Traditional Security Fails
Traditional security frameworks were built on the assumption that the server is a fortress—a controlled, hardened environment where the organization dictates every variable. In this legacy model, developers focus on protecting the gates through firewalls and input sanitization, safe in the knowledge that the core logic remains hidden behind the data center walls. However, the mobile revolution has inverted this dynamic. When a mobile application is deployed, the entire “gate” and much of the “fortress” logic are packaged into a binary and handed directly to the end user. This physical access invalidates the core tenets of the past decade of cybersecurity, as the client is no longer an ephemeral browser window but a complex, persistent piece of software subject to local interrogation.
Once the binary resides on a device, it is no longer protected by the organization’s infrastructure. Sophisticated attackers can use static and dynamic analysis to map out the application’s internal workings, identifying API endpoints, hardcoded secrets, and logical flows that were never intended for public consumption. Traditional Static Application Security Testing (SAST) often fails here because it looks for flaws in the code rather than flaws in the environment where that code will live. A perfectly written piece of code can still be compromised if the environment it runs in is manipulated to bypass its security checks. Consequently, the focus must shift from merely writing secure code to ensuring that the code can detect and respond to its own subversion when it inevitably lands in a hostile setting.
Furthermore, the fragmentation of mobile operating systems and hardware versions complicates the task of maintaining a consistent security posture. While a web developer targets a few major browsers, a mobile developer must account for thousands of device configurations, many of which may have unpatched vulnerabilities or customized kernels. This lack of environmental uniformity means that a security control that works on a flagship device might be easily bypassed on a budget model or a device running a custom ROM. The “messenger” must therefore be equipped with its own internal sensors to evaluate the integrity of its surroundings before performing any sensitive operations. This self-awareness is the only way to maintain a semblance of security in a landscape where the developer has zero control over the hardware.
The 43% Reality Check: Mobile as the New Enterprise Edge
The shift toward decentralized operations has transformed mobile devices from simple tools of convenience into the primary targets for enterprise breaches. Current industry data suggests that approximately 43% of organizational security incidents now originate at the mobile edge, reflecting a massive migration of high-value data to portable, less-regulated devices. As we navigate the period from 2026 to 2028, the industry is increasingly realizing that standard DevSecOps pipelines, originally architected for centralized web services, are fundamentally unequipped to handle this fragmentation. The divergence between “server-side safety” and “device-side exposure” has created a blind spot that attackers are exploiting with increasing frequency and sophistication.
This “reality check” is forcing a change in how chief information security officers view the mobile app. It is no longer a peripheral interface; it is the most vulnerable point of contact between the organization and its customers. The speed of mobile development cycles often outpaces the ability of security teams to perform deep manual reviews, leading to a reliance on automated tools that were never designed for the unique challenges of mobile binaries. When a breach occurs at the mobile edge, it is rarely due to a simple SQL injection; instead, it is often the result of credential harvesting from local storage or the manipulation of business logic within the app’s memory. These are mobile-specific problems that require mobile-specific DevSecOps interventions.
Closing the gap between development speed and data security requires a shift in how resources are allocated within the pipeline. It is no longer sufficient to treat mobile security as a final checkbox before an app store submission. Instead, security must be integrated into the very fabric of the build process, with a focus on how the app will behave in an untrusted state. This involves moving beyond basic vulnerability scanning to include simulations of device compromise and binary tampering. By acknowledging the mobile edge as the new front line of enterprise defense, organizations can begin to deploy the specialized tools and methodologies needed to protect their data in an increasingly mobile-centric world.
Navigating the Three Critical Blind Spots of Modern Pipelines
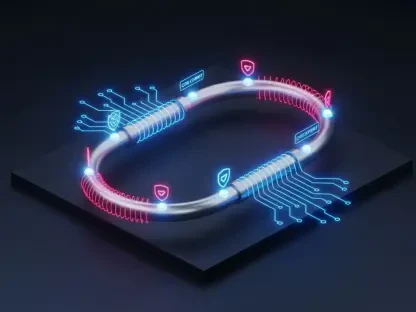
To truly fortify a mobile application, development teams must address specific technical vulnerabilities that standard testing suites frequently overlook. The first of these is the rise of Man-at-the-End (MATE) attacks, where an attacker who physically possesses the device uses dynamic instrumentation to manipulate the app. Tools like Frida allow an adversary to inject code into an application’s memory at runtime, effectively rewriting the app’s behavior while it is running. To counter this, developers must move beyond static obfuscation and implement Runtime Application Self-Protection (RASP). This involves active memory scanning to detect “trampolines” or hooks and utilizing hardware-backed attestation APIs to ensure the operating system confirms the device’s integrity.
The second major blind spot involves the persistent fallacy of software-only cryptography. Many teams still store sensitive keys in “private” software sandboxes, like the standard iOS Keychain or Android Keystore, without enforcing hardware-level protections. On a compromised or rooted device, these keys can be extracted via memory dumps or specialized exploitation techniques. To solve this, developers must force encryption keys to reside within the Trusted Execution Environment (TEE) or the Secure Enclave, ensuring the keys never enter the application’s accessible memory. Additionally, requiring a physical biometric prompt for key access ensures that data remains encrypted even if a device is stolen while in an unlocked state.
Finally, the rise of AI-assisted development has introduced a new form of “logic entropy” into mobile codebases. While AI assistants can significantly speed up the coding process, they often suggest boilerplate code that includes outdated patterns or insecure network configurations. AI-generated code frequently misses nuances like certificate pinning or uses deprecated cryptographic libraries that “work” but offer no real protection. Addressing this requires custom linting rules designed to flag common AI shortcuts and a mandatory Software Bill of Materials (SBOM) enforcement. By validating every AI-suggested dependency against known vulnerability databases, teams can prevent the accidental introduction of systemic weaknesses into their applications.
Combatting the Rise of iOS Sideloading and Repackaging
Recent regulatory shifts have inadvertently opened a massive new vector for repackaging attacks on platforms that were previously considered relatively secure. With the increased ability for users to sideload applications from third-party sources, attackers can now more easily intercept a legitimate application, inject malicious surveillanceware, and re-sign it with a valid—albeit unauthorized—developer certificate. This repackaging allows an attacker to distribute a fully functional version of a popular app that simultaneously exfiltrates user data in the background. Because the app appears legitimate and is signed by a valid certificate, many standard operating system protections are bypassed, leaving the user and the organization at risk.
To combat this trend, mobile applications must be designed to perform runtime certificate fingerprinting as a core security function. This involves the application checking its own signing identity during execution and comparing the active certificate against a hardcoded hash of the official production key. If a mismatch is detected—indicating the app has been re-signed by an external party—the application should self-terminate or disable access to sensitive features. This internal integrity check is the only way to ensure the app has not been tampered with after leaving the developer’s control. It essentially turns the application into its own watchdog, protecting the brand and the user from the dangers of the secondary market.
Furthermore, the shift toward open app ecosystems requires a more robust approach to data isolation. If an app can no longer rely on the operating system to prevent sideloading, it must rely on itself to ensure its data is not accessible to other, potentially malicious, sideloaded apps. This means implementing stricter local encryption and ensuring that any sensitive logic is moved to the backend wherever possible. By assuming that the device may contain multiple unverified applications, developers can create a siloed environment within the app that maintains its integrity regardless of what other software is installed on the device.
Practical Frameworks for a Hostile Runtime Environment
Addressing these vulnerabilities requires a fundamental shift in the DevSecOps mindset, prioritizing resilience over mere bug-hunting. One practical strategy is the implementation of what can be called a “performance tax.” Security measures like RASP, deep obfuscation, and hardware-backed encryption inevitably introduce some level of latency and CPU load. In the past, these were often avoided to ensure a buttery-smooth user experience. However, modern teams must embrace this tax as a necessary cost of doing business in a high-risk environment. The goal is to ensure that the computational and financial cost to an attacker of extracting data is significantly higher than the value of the data itself.
Moreover, modern pipelines must operate under a zero-trust mobile protocol. This framework assumes that every device is compromised from the start. Under this model, local data storage is minimized, and any data that must be stored on the device is cryptographically bound to the specific hardware rather than just the user’s account. This prevents an attacker from simply copying a local database to another device for analysis. By ensuring that the application’s core functionality is contingent on a successful environment check, organizations can prevent their apps from becoming a bridge for attackers to reach internal enterprise systems.
The transition to these advanced security frameworks was not an easy shift for many development teams. It required a significant overhaul of the build process and a commitment to continuous monitoring after deployment. Organizations that successfully adopted these measures found that they were able to detect and mitigate threats in real-time, often before any data was actually compromised. The integration of hardware-backed attestation and rigorous AI-code auditing became standard practices that defined the leaders in the mobile space. Ultimately, the industry moved toward a more mature understanding of the mobile binary, treating it not as a static file, but as a dynamic entity that must constantly defend its own existence in a lawless digital landscape. This proactive stance ensured that even as the complexity of attacks grew, the defenses evolved at a matching pace, securing the future of the mobile-first enterprise.