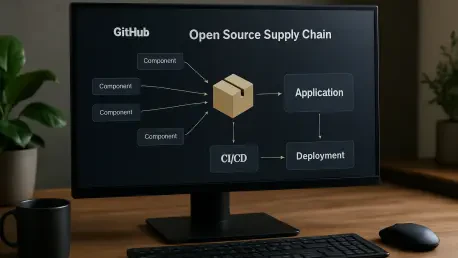
The modern software landscape faces an unprecedented challenge as the focus of cyberattacks shifts from direct code manipulation to the sophisticated theft of developer credentials within the primary supply chain. Attackers are no longer content with merely injecting malicious snippets into individual files; they now actively hunt for API keys, environment secrets, and authentication tokens that reside within high-velocity development environments. By successfully hijacking these sensitive credentials, a malicious actor can impersonate a trusted maintainer, gaining the ability to publish poisoned package updates that appear entirely legitimate to the end-user. This method of infiltration creates a dangerous ripple effect across the global ecosystem, as a single compromised library can silently infect millions of downstream applications during routine dependency updates. Consequently, the industry is moving toward a defensive posture that prioritizes the hardening of the underlying infrastructure that facilitates code automation and package distribution, rather than simply monitoring the code itself for obvious signs of tampering or suspicious behavior.
Workflow Hardening and Automated Defense Mechanisms
Securing the automation layer requires a deep understanding of how GitHub Actions can be inadvertently turned against a project. Many repositories remain vulnerable because they use triggers that grant high-level permissions to code coming from external contributors, such as those submitting pull requests. If a workflow is configured to execute scripts or perform deployments based on untrusted input, it becomes a prime target for exfiltration attacks designed to leak repository secrets. To counter this, maintainers must implement rigorous code reviews specifically for their YAML configuration files, ensuring that no execution path allows for arbitrary command injection. Automated scanning tools, such as CodeQL, play a vital role here by performing semantic analysis to identify common security anti-patterns that a human reviewer might miss during a busy development cycle. These tools provide a consistent baseline for security, flagging potential leaks before they can be exploited in a production-like environment.
Beyond the initial configuration of workflows, the integrity of a project depends heavily on the external actions it consumes. A critical best practice for any serious open-source project is the move toward strict dependency pinning, which necessitates referencing third-party actions by their unique, immutable commit SHA rather than by mutable version tags like “@v1” or “@latest.” Because version tags can be updated by an action’s owner to point to entirely different code—either intentionally or following an account compromise—relying on them introduces a significant element of risk. By pinning to a specific SHA, a maintainer guarantees that the workflow only ever executes the exact version of the code that has been previously audited and approved. This level of granularity prevents “set and forget” workflows from becoming a vector for silent supply chain poisoning. Furthermore, sanitizing all user-generated data, including branch names and issue titles, ensures that malicious scripts cannot be injected into the automated build process, effectively closing a common door for credential theft.
Advancing Ecosystem Integrity Through Trusted Publishing
The most transformative shift in the current security paradigm involves the systematic elimination of long-lived static secrets through the adoption of Trusted Publishing. Historically, developers have relied on permanent API tokens stored as environment variables to publish their work to registries like npm. This traditional model is inherently fragile because once a secret is stolen, it remains valid until the owner manually revokes it, providing attackers with a wide window of opportunity to distribute malicious updates. By transitioning to a system powered by OpenID Connect (OIDC), GitHub Actions can now request short-lived, scoped tokens that exist only for the duration of a specific deployment job. This approach uses a workload identity to verify that the request is coming from a pre-authorized repository and workflow, removing the need for a developer to ever handle or store a persistent credential. This change drastically reduces the attack surface, making it nearly impossible for an adversary to gain unauthorized publishing rights through credential exfiltration alone.
This architectural evolution does more than just secure individual accounts; it enhances the collective security of the entire npm registry by providing a transparent and verifiable audit trail. When a package is configured for Trusted Publishing, any attempt to upload a new version using a traditional, static API key acts as a high-fidelity alarm for the community. Such a discrepancy indicates that the standard, secure path was bypassed, signaling a likely compromise of a maintainer’s legacy credentials. This visibility allows security teams and automated monitors to respond with much greater speed, potentially freezing suspicious updates before they are widely downloaded. As more projects move toward this OIDC-based identity model, the reliance on manual secret rotation becomes a thing of the past. The resulting infrastructure is not only more resilient against targeted attacks but also sets a new standard for how modern software should be delivered to the public. This shift marks a move away from trusting individual developers to manage complex security secrets and toward a platform-level assurance that guarantees the origin and integrity of every published package.
Strategic Implementation and Resilience Strategies
Building a resilient supply chain requires a proactive commitment to continuous monitoring and the rapid adoption of emerging security standards. Organizations and independent maintainers should prioritize the integration of the GitHub Advisory Database into their daily routines to receive immediate notifications about vulnerabilities in their dependency trees. This proactive stance ensures that when a popular library is flagged as part of a malware campaign, the affected teams can initiate a patch or roll back to a known-safe version within minutes. The implementation of mandatory two-factor authentication for all package maintainers serves as another vital layer of defense, significantly raising the cost of entry for attackers. These measures, while effective, are most successful when they are treated as part of a holistic strategy that includes regular audits of the entire build pipeline and a willingness to adopt more restrictive security defaults as they become available on the platform.
Looking ahead, the focus must remain on reducing the friction associated with these security upgrades to ensure widespread adoption. The transition to a more secure open-source world was characterized by a collaborative effort between platform providers and the developer community. To maintain this momentum, maintainers should evaluate their existing projects for legacy configurations and begin the migration to short-lived tokens and SHA-pinned actions immediately. These actions are not merely technical adjustments; they represent a fundamental change in how the community views its responsibility toward the users who rely on their code. By embracing these architectural improvements and staying informed about the latest malware detection techniques, developers can build a more robust foundation for the software that powers global infrastructure. The ultimate goal is to create an environment where the supply chain is no longer the weakest link, but a hardened pathway that ensures the safety and reliability of software for everyone. This objective was successfully met by transforming security from a manual burden into a built-in feature of the development lifecycle.