The modern smartphone has evolved into a high-stakes battleground where the traditional defenses of a few years ago no longer hold weight against the current tide of decentralized distribution. This year marks a definitive turning point for the mobile ecosystem as the long-standing concept of the walled garden officially collapses. Organizations now face a frontier where security is no longer a perimeter-based concern but an application-centric necessity. The shift from a centralized authority to a decentralized market has forced a fundamental rethink of how data is protected. Stakeholders, ranging from global regulators to enterprise security leaders, are now navigating a world where AI-driven interactions are the baseline for every mobile experience.
Navigating the Fragmented Frontier of Modern Mobile Defense
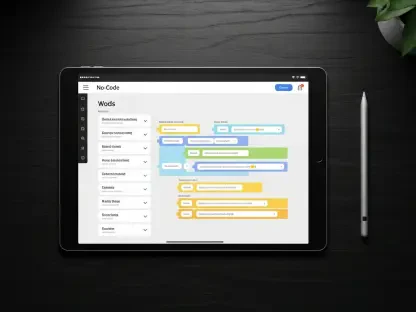
The transition toward a decentralized mobile market has redefined the role of security within the enterprise. Previously, gatekeepers like major operating system providers offered a predictable level of safety through curated app stores. However, the current reality involves a diverse array of distribution channels that bypass these traditional filters. This fragmentation demands that security professionals focus on building resilience directly into the applications themselves rather than relying on the platform to provide a safety net. Application-centric security ensures that even when a device operates within an untrusted environment, the core data remains shielded from external interference.
This new landscape places immense pressure on AI developers and security leaders to coordinate their efforts more closely than ever before. The ubiquity of AI-driven interactions means that every mobile touchpoint is a potential entry for sophisticated automated threats. Consequently, the defense strategy has shifted from a reactive posture to one of proactive monitoring and autonomous response. Global regulators have recognized this change, pushing for frameworks that prioritize user privacy without stifling the innovation that decentralized markets provide. The challenge lies in balancing these competing interests while maintaining a robust defense against increasingly capable adversaries.
Technological Accelerants and the New Economics of App Risk
Emerging Trends in Decentralized Distribution and AI-Augmented Development
Legislative mandates such as the Digital Markets Act have successfully opened the doors to alternative app marketplaces and web-based distribution models. While this fosters a competitive environment, it also introduces a significant level of hidden risk. The transition from centralized gatekeeping to fragmented governance means that third-party software development kits often find their way into the mobile supply chain without sufficient oversight. These components frequently harbor vulnerabilities that remain undetected until they are exploited in a live environment. The lack of a single point of authority makes it difficult to enforce a uniform security standard across all available applications.
The integration of artificial intelligence into the software development lifecycle has become a double-edged sword for the industry. On one hand, AI enables developers to ship code at an unprecedented speed, meeting the demands of a high-velocity market. On the other hand, this rapid pace often results in the inclusion of inherent security flaws that automated tools might overlook. The tension between development speed and code integrity is a primary driver of risk in the current ecosystem. Balancing the benefits of AI-augmented development with the necessity of rigorous security testing is the central struggle for modern DevSecOps teams.
Market Projections and the Escalating Cost of Mobile Vulnerabilities
Forecasts regarding the mobile attack surface indicate a period of sustained growth from 2026 through the end of the decade. As more critical functions move to mobile platforms, the financial incentives for attackers continue to rise. This has led to a significant shift in corporate security spending, with budgets moving away from legacy scanning tools that only look for known signatures. Instead, investment is flowing into real-time, in-app protection mechanisms that can detect and neutralize threats as they occur. The market now values the ability to respond to zero-day exploits in seconds rather than days or weeks.
Data-driven performance indicators show a widening gap between organizations that have adopted AI-enhanced DevSecOps and those sticking to traditional models. Companies utilizing advanced automation for vulnerability detection and remediation report significantly lower costs associated with security breaches. Moreover, these organizations demonstrate greater agility in responding to new regulatory requirements and market shifts. The economics of mobile security now dictate that proactive investment in embedded defenses is far more cost-effective than the reactive cleanup of a successful breach. The cost of a single vulnerability has reached a level where it can threaten the very viability of a digital business.
Crucial Hurdles in an Era of High-Velocity Exploitation
The volatility of AI-generated code remains a primary concern for security architects who must manage the black box nature of automated remediation. When AI tools identify and fix vulnerabilities, they often do so without providing a clear rationale, making it difficult for human auditors to verify the integrity of the solution. This lack of transparency can lead to a false sense of security where underlying logic flaws remain hidden. Furthermore, the speed at which AI can generate new code variants means that traditional testing cycles are often outdated by the time an application is actually deployed to the end user.
A widening talent gap continues to plague the industry, as the demand for specialized mobile security expertise far outstrips the available supply. There is a dangerous trend toward over-reliance on AI as a complete substitute for human judgment, which often leads to catastrophic oversights. While AI can handle repetitive tasks and large-scale data analysis, it lacks the contextual understanding required to counter hyper-personalized social engineering or novel offensive tactics. Strategic resilience requires a combination of automated power and human intuition to identify the subtle signals of a sophisticated breach. Organizations must invest in training their workforce to work alongside AI rather than expecting the technology to function in a vacuum.
The Global Regulatory Overhaul and Compliance Mandates
The impact of the EU Digital Markets Act has resonated far beyond Europe, influencing similar frameworks in Japan, the United Kingdom, and other major economies. These regulations have fundamentally changed the relationship between platform providers and application developers. Compliance is no longer a matter of checking a few boxes during the submission process; it now requires a continuous commitment to transparency and user protection. Regulators are increasingly focused on the security of the distribution process itself, ensuring that alternative stores do not become a conduit for large-scale malware campaigns.
In many jurisdictions, mobile applications are now being classified as critical infrastructure, particularly within the financial sector. Authorities such as the Monetary Authority of Singapore and the Reserve Bank of India have introduced stringent mandates that require financial apps to feature continuous runtime monitoring. These requirements move beyond static security assessments and demand that applications prove their integrity throughout their entire lifecycle. The evolution of compliance now includes mandatory notarization and proof of anti-tampering technology for any application handling sensitive user data or large-scale financial transactions.
The Road Ahead: Innovation and Strategic Resilience
The rise of self-defending apps represents the next logical step in the evolution of mobile security technology. These applications integrate autonomous runtime protection that can identify and block unauthorized access attempts without needing a connection to a central server. This technology is becoming essential as mobile devices move into environments with intermittent connectivity or where low-latency response is critical. By embedding security directly into the application binary, developers can ensure that the software remains protected regardless of the underlying platform or the network it uses.
Future market disruptors such as the convergence of 6G, edge computing, and generative AI will further redefine how we handle mobile identity. Authentication is moving away from static passwords and toward continuous, behavior-based verification that happens at the edge of the network. This shift will provide a more seamless user experience while simultaneously increasing the difficulty for attackers to impersonate legitimate users. Preparing for a zero-trust mobile future requires organizations to embrace these technologies while remaining mindful of shifting consumer privacy expectations and the pressures of the global economy.
Strategic Synthesis and the Blueprint for 2026 Security
The transformation of the mobile landscape into a high-velocity and decentralized environment required a complete overhaul of traditional defense strategies. Leaders recognized that the collapse of walled gardens removed the primary safety net that many enterprises had relied upon for over a decade. This shift necessitated an immediate move toward embedded security and adaptive governance to maintain a competitive edge. The industry moved away from reactive postures, instead prioritizing the integration of autonomous protection directly within the application code to counter the speed of AI-driven offensive tactics.
Enterprises successfully navigated this transition by balancing the rapid shipping of code with responsible AI oversight. They prioritized human leadership to fill the contextual gaps that automated tools inherently possessed. The shift in regulatory frameworks across the globe turned compliance into a continuous process of runtime monitoring rather than a static checklist. Ultimately, the organizations that thrived were those that treated mobile security as a foundational element of their innovation strategy rather than a secondary consideration. This period demonstrated that true strategic resilience stemmed from the harmonious blend of technological power and rigorous human expertise.