The modern digital landscape has reached a point where the sudden disappearance of a personal or professional database is no longer a remote possibility but an inevitable statistical certainty for many users. On March 31st, World Backup Day 2026 serves as a global catalyst for addressing the fragility of our collective digital existence, which is increasingly threatened by sophisticated cyberattacks and hardware entropy. Consider the impact of losing an entire career’s worth of intellectual property or decades of family photographs due to a single mechanical failure or a lapse in security protocol. This day is not merely a symbolic observance but a practical intervention aimed at reducing the percentage of users who lose everything because they lacked a redundancy plan. Statistics from recent industry reports indicate that nearly thirty percent of people have never backed up their files, even as ransomware tactics become more aggressive and pervasive in the current technological climate.
The Evolving Nature of Digital Threats in 2026
The Escalation: Sophisticated Cyber Attacks
The rise of automated ransomware-as-a-service platforms has commodified digital extortion, making it possible for low-level actors to target individuals and small businesses with alarming precision. These malicious entities frequently target local files and synced cloud drives, rendering traditional single-layer protection methods insufficient for modern safety standards. As we navigate the complexities of 2026, the prevalence of polymorphic malware means that threats can remain dormant within a system for weeks, quietly encrypting data before a user even realizes a breach has occurred. This reality transforms the act of backing up from a passive task into a strategic necessity that requires constant vigilance and updated security definitions. Without a disconnected or immutable copy of essential information, victims are often left with no recourse other than paying exorbitant sums to anonymous attackers. The psychological and financial toll of such events underscores why proactive data preservation remains the most effective defense against the current surge in high-tech criminality.
Beyond external attacks, the integrity of the data being saved has become a primary concern for cybersecurity professionals who emphasize that a backup is only as good as the files it contains. Implementing a backup strategy on a system that is already compromised by hidden malware effectively archives the threat, allowing it to propagate when the data is eventually restored. To mitigate this risk, modern protocols now demand that all files undergo rigorous real-time antivirus scanning prior to being moved to long-term storage or secondary drives. This verification process ensures that the “clean” state of a system is what is actually being preserved, preventing the accidental re-infection of new hardware during a recovery phase. The synergy between active threat detection and passive storage creates a comprehensive safety net that protects the user from both the loss of data and the persistence of malicious software. Ensuring that the backup source is untainted is now recognized as a non-negotiable step in maintaining a truly secure and recoverable digital environment for any professional.
Hardware Reliability: Physical Degradation Issues
While the focus often shifts toward digital threats, the physical components that house our information are subject to inevitable mechanical wear and the limitations of modern semiconductor physics. Solid-state drives and high-capacity NVMe modules, while significantly faster than traditional hard disks, possess a finite number of write cycles before the NAND flash memory cells begin to degrade permanently. In the high-demand environments of 2026, where massive datasets and high-resolution media are the norm, these limits are reached more quickly than in previous hardware generations. Sudden electrical surges, manufacturing defects, or even simple overheating can cause catastrophic controller failure, leading to total data loss without any prior warning signs. This inherent vulnerability of physical hardware means that relying on a single device, no matter how advanced or expensive it may be, is a fundamental gamble with one’s digital legacy. Understanding the lifecycle of storage media is crucial for timing hardware rotations and ensuring that data is migrated to fresh drives before the older units reach their anticipated failure thresholds.
Environmental factors and human error also play significant roles in the physical destruction of data, often occurring in ways that software-based protections cannot prevent. Floods, fires, and accidental drops can instantly destroy a laptop or external drive, highlighting the necessity of off-site storage solutions that remain physically separate from the primary workstation. Even in a controlled office setting, the simple act of misplacing a small flash drive or having a device stolen can lead to the permanent loss of sensitive information if no secondary copy exists. These physical risks demonstrate why a localized backup, though convenient and fast, is only one component of a larger, more resilient safety architecture. By diversifying the physical locations and formats where data is stored, individuals can effectively shield their information from localized disasters that might otherwise result in total loss. The realization that hardware is temporary while data is intended to be permanent should drive the adoption of more robust and geographically distributed storage practices across all sectors of the modern economy.
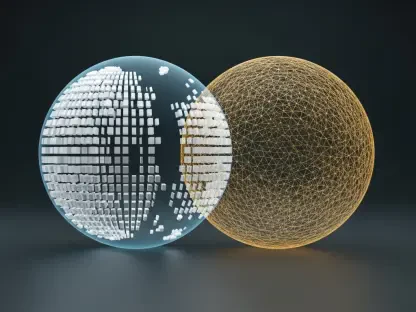
Diversifying Storage Strategies for Maximum Protection
Strategic Choices: Cloud and Local Storage Solutions
The choice between cloud-based services and local physical storage involves a complex trade-off between convenience, recurring costs, and the ultimate control over one’s private data. Cloud providers offer the advantage of seamless background synchronization and accessibility from any device globally, which is essential for the mobile and distributed workforce of 2026. However, these services often involve ongoing subscription fees that can accumulate significantly over time, and they introduce a layer of third-party risk regarding privacy and data sovereignty. Users must carefully scrutinize service level agreements to understand how their information is encrypted and who holds the decryption keys in the event of a provider-side breach. Despite these concerns, the cloud remains a powerful tool for off-site redundancy, as it automates the backup process and removes the burden of manual hardware management from the user. For many, the peace of mind offered by professional-grade data centers—which feature their own internal redundancies and security protocols—outweighs the potential drawbacks of relying on a centralized service provider.
In contrast, local storage solutions such as high-capacity external drives and direct-attached storage units provide a level of speed and data ownership that cloud services cannot match. These offline backups are immune to remote hacking attempts when disconnected, making them the preferred choice for sensitive financial records, proprietary software, or high-definition media archives. The absence of monthly fees makes this a cost-effective long-term strategy, though it places the entire responsibility for maintenance and physical security on the individual owner. One significant challenge with local drives is the need for a disciplined manual routine or specialized software to ensure that the backups are performed consistently and on schedule. Furthermore, the risk of physical damage or loss remains a constant threat, necessitating that these drives be stored in secure, temperature-controlled environments to prevent bit rot or component failure. Balancing the high-speed access of local hardware with the security of an offline state creates a formidable barrier against the most common causes of data destruction and digital theft in today’s world.
Modern Implementation: Hybrid Models and NAS Systems
Network Attached Storage (NAS) devices have emerged as a sophisticated middle ground, offering the benefits of local physical ownership combined with the remote accessibility typically associated with cloud services. These systems allow users to create their own “private cloud,” where data is stored on a centralized server within the home or office network and can be accessed securely via the internet. In 2026, the latest NAS units feature advanced RAID configurations that provide internal redundancy; if one drive fails, the system can rebuild the data from the remaining disks without any loss. This level of resilience is particularly valuable for small businesses and creative professionals who handle large volumes of data that would be too slow or expensive to upload to a standard cloud provider. However, because a NAS is connected to the network, it requires diligent firmware updates and strong firewall configurations to prevent it from becoming a target for network-based attacks. The complexity of setting up and maintaining a NAS is often offset by the long-term savings and the superior control it grants over the entire data lifecycle.
Effective digital safety in 2026 was ultimately achieved by those who adopted the 3-2-1 backup rule, which stipulated maintaining three copies of data on two different media types, with one copy kept off-site. This methodology ensured that no single point of failure—whether a hardware crash, a house fire, or a sophisticated ransomware strain—could result in the permanent erasure of critical information. Moving forward, the focus transitioned from simply creating backups to verifying their integrity through regular restoration tests and automated checksum validations. Organizations and individuals alike realized that a backup is only useful if it can be successfully deployed during a crisis, leading to a shift toward more proactive and managed storage ecosystems. The lessons learned during this period emphasized that data preservation is an ongoing commitment rather than a one-time setup, requiring a mix of hardware reliability and software intelligence. By integrating these diverse strategies into a cohesive plan, the modern user successfully immunized their digital life against the unpredictable nature of the technological world, turning potential catastrophes into manageable inconveniences.