Anand Naidu is a seasoned development expert with a deep mastery of both frontend and backend architectures. With years of experience navigating the complexities of enterprise computing, he specializes in bridging the gap between core language development and the practical application of frameworks in large-scale environments. In this conversation, we explore the implications of Oracle’s recent launch of the Java Verified Portfolio and how it redefines the way development teams manage their software supply chains.
The discussion centers on the strategic shift toward a curated ecosystem of Oracle-supported tools, including JavaFX and Helidon, which sit alongside the core JDK. We examine how this initiative simplifies licensing, enhances security through governed dependencies, and provides a clear roadmap for enterprise-grade applications. Anand shares his perspective on the practical steps for integration and the long-term benefits of aligning with a verified stack in cloud-native environments.
The Java Verified Portfolio provides a curated set of tools like JavaFX and the Helidon framework outside the core JDK. How does this curation affect your selection of UI and microservices libraries, and what are the specific steps for integrating these Oracle-supported assets into an existing pipeline?
This curation fundamentally changes the risk assessment for architects because it moves us away from the “wild west” of community-driven libraries toward a stack with guaranteed longevity. When I look at Helidon for microservices or JavaFX for UI, I’m no longer just looking at features; I’m looking at the lifecycle management and roadmap transparency that Oracle now provides. To integrate these into a pipeline, the first step involves auditing your current dependencies to identify where unsupported open-source libraries can be swapped for JVP-verified counterparts. Next, you pull the verified binaries from preferred download sites, ensuring you map them to the correct JDK compatibility versions as specified in the JVP documentation. Finally, you update your CI/CD build scripts to reference these governed assets, allowing your security scanners to recognize them as trusted, Oracle-backed components rather than high-risk third-party code.
Separating core JDK licensing from supplemental tool support aims to simplify roadmap planning for development teams. In a large enterprise environment, how do you manage the trade-offs between these different support timelines, and what metrics should be used to measure the success of this streamlined licensing model?
Managing these trade-offs requires a two-tiered governance strategy where we decouple the foundational runtime updates from the more rapid evolution of frameworks like Helidon. In a large enterprise, this separation is a relief because it means a framework update doesn’t necessarily force a high-stakes migration of the entire JDK, which often involves thousands of legacy lines. We measure the success of this model by tracking the “mean time to patch” and the reduction in legal overhead related to license audits. If our compliance team spends 30% less time chasing down disparate licenses because the JVP and JDK are now clearly delineated under a unified support umbrella, that’s a massive win for operational velocity.
Organizations often face significant security risks when relying on unsupported open-source libraries within their supply chain. How does migrating to a governed portfolio of tools improve your security posture, and what anecdotes can you share regarding the pitfalls of managing unverified or disparate Java dependencies?
Migrating to a governed portfolio creates a “circle of trust” that significantly hardens the software supply chain against vulnerabilities like the ones we’ve seen paralyze industries in recent years. When you use unverified dependencies, you are essentially betting your company’s reputation on the maintenance habits of a few volunteers who might abandon a project at any time. I remember a project where a critical production bug was traced back to a tiny, “handy” open-source utility that hadn’t been updated in three years; we had to rewrite the entire module under extreme pressure because there was no official support to turn to. With the Java Verified Portfolio, you have the backing of the Java Platform Group, meaning if a security flaw is found in an included framework, there is an official, enterprise-grade fix rather than a desperate wait for a community patch.
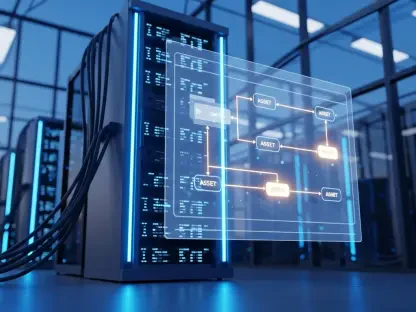
These verified assets are now accessible at no extra cost for those using specific cloud workloads or subscriptions. How does this financial model change the decision-making process for developers choosing between various VS Code extensions, and what long-term integration benefits does this provide for high-scale cloud applications?
The fact that the Java Platform extension for VS Code and other assets are included at no extra cost for OCI and Java SE subscribers removes the “friction of procurement” that often stalls technical progress. Developers are no longer forced to choose between a free but limited tool and a paid professional extension; they can go straight to the high-performance, Oracle-supported option. For high-scale cloud applications, this creates a seamless bridge between the local development environment and the Oracle Cloud Infrastructure (OCI) production environment. This consistency ensures that the code running on a developer’s laptop behaves exactly the same way when it scales to millions of users in the cloud, reducing the “it works on my machine” syndrome that plagues large-scale deployments.
As more technologies are added to this portfolio over time, the landscape for Java developers will continue to shift. What criteria should a lead architect use to evaluate which new tools to adopt, and how can teams ensure their tech stacks remain compatible with these evolving lifecycle management standards?
A lead architect must evaluate new additions based on three pillars: ecosystem alignment, long-term support (LTS) windows, and the specific JDK compatibility mapping provided by the JVP. You shouldn’t just adopt a tool because it’s “new”; you adopt it because it fits into the governed lifecycle that Oracle has committed to supporting. To stay compatible, teams should treat the JVP roadmap as a North Star for their internal tech radar, scheduling “alignment sprints” whenever a major portfolio update is released. By proactively staying within the supported versions of the portfolio, organizations avoid the technical debt that accumulates when frameworks and runtimes drift too far apart.
What is your forecast for the Java Verified Portfolio?
I forecast that the Java Verified Portfolio will become the standard blueprint for “Safe Java” in the enterprise, eventually expanding to include more robust data-handling libraries and perhaps even AI-integration frameworks. As more developers realize the value of having a single point of accountability for their entire stack—from the IDE extension down to the microservices framework—we will see a consolidation of the currently fragmented Java ecosystem. Within the next few years, I expect the JVP to be the primary reason organizations choose Oracle over generic OpenJDK distributions, as the peace of mind offered by a fully governed supply chain becomes more valuable than the tools themselves.