The Stakes: Why CI/CD Needs Runtime Defense
Build systems now compile code at cloud speed while attackers slip payloads through allow-listed, encrypted egress that traditional scanners never see until damage is done, and that shift in attack timing has turned the live build phase into the most critical, least-observed surface in modern delivery pipelines. Static code analysis, software composition analysis, and cloud posture tools remain essential, but they watch before or after the moment that truly matters: when a build reaches out to the network, resolves packages, runs scripts, and can quietly leak credentials.
InvisiRisk’s Build Application Firewall (BAF) set out to close that blind spot by enforcing policy and inspecting packets during execution. Version 1.1.38 sharpened that proposition with controls aimed at covert exfiltration and with richer evidence about what a build actually consumed. The review below evaluates how those choices performed, what trade-offs emerged, and why this approach differs from adjacent tools vying to secure the software supply chain.
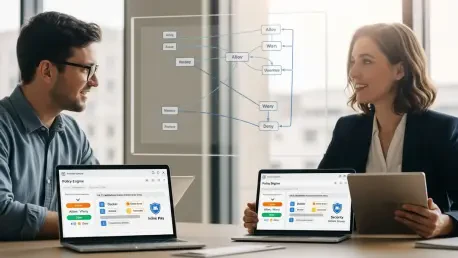
How It Works: Inline Proxy, Policy Engine, and TruSBOM
BAF inserts an inline proxy/agent into build jobs, mediating outbound connections and applying policy in real time. Unlike egress filters that only see destinations, BAF parses request bodies and headers to evaluate intent: Which registry is contacted, which artifact is fetched, which payload is being posted, and whether any of it matches known encodings of secrets. The policy engine decides allow, warn, or deny, and the telemetry layer correlates network events with build metadata to produce actionable context.
The second pillar is runtime-derived provenance. Rather than trusting manifests or cached configuration, BAF assembles a dependency graph from what the build actually pulled—direct, transitive, and cached layers—across ecosystems like RubyGems, Debian, and Alpine. InvisiRisk brands this the “TruSBOM,” arguing that a bill of materials is only credible if it mirrors run-time resolution, not just declared intent. In practice, that distinction matters when caches mask version drift or when transitive packages add unexpected risk.
What’s New in v1.1.38: Encoded Secrets and Live Traffic Control
The headline change in v1.1.38 was encoded secret interception. Campaigns such as TeamPCP and Shai-Hulud have normalized hiding credentials inside Base64, double-Base64, or layered encodings, often tunneled to trusted endpoints. BAF now detects and blocks those patterns within request bodies and headers as traffic leaves the build, closing a bypass that defeated systems focused solely on destinations or post-facto logs.
Crucially, this control was designed to operate even when traffic targeted allow-listed registries or moved through encrypted channels. Because the proxy lives inside the job, it can inspect content before TLS encapsulation, making prevention feasible where external perimeter devices only see ciphertext. This is the practical meaning of “runtime enforcement”: intervening at the exact frame when the secret would otherwise escape.
Dependency Truth: Runtime-Derived Graph and Vulnerability Attribution
The TruSBOM functionality advanced beyond visualization. By observing fetches and cache hits, BAF reconstructed a ground-truth graph that often diverged from manifests used by SCA tools. That allowed ecosystem-specific vulnerability attribution: a CVE tied to a RubyGem was not double-counted when the same code also appeared in a Debian package, reducing alert fatigue and clarifying which node in the chain carried the liability.
For teams wrestling with provenance questions—Which package version actually influenced this binary? Did a cached layer bypass pinned constraints?—the runtime graph offered decisive evidence. The value here was less about pretty diagrams and more about enabling confident remediation and precise exceptions that do not over-broaden risk acceptance.
CI Integration: Hardened GitHub Actions Across Standard and Docker
A security control is only as useful as its coverage. BAF’s GitHub Actions integration expanded automatic insertion to Docker-based workflows alongside standard jobs, minimizing the historical gap where containerized steps escaped runtime observation. Reliability improvements—pre-run validation, multi-account org support, lifecycle notifications—reduced brittle setup patterns that previously produced blind spots.
Configuration now followed two paths: a GitHub App for automation and a YAML-driven, policy-as-code model. That duality recognized cultural reality. Some platform teams prioritize central guardrails; others prefer repository-local control with reviews. In both modes, the barrier to adoption felt lower, and importantly, rollouts did not choke developer velocity during early tuning.
Policy Intelligence: AI, Signal Quality, and Operator UX
The AI-assisted policy engine did not try to be a black-box oracle. Instead, it generated candidate policies based on observed traffic, then applied warn or deny modes so teams could calibrate impact. Enforced unique naming and streamlined assignment prevented configuration drift—a common, non-obvious failure mode when policies proliferate across repos and environments.
Signal quality mattered as much as raw detection. Tuned anomaly models reduced false positives on high-volume build traffic, preserving trust that a deny was worth interruption. The design choice to make AI advisory, not absolute, was pragmatic: operators retained control while benefiting from pattern recognition across thousands of jobs.
Performance and Trade-Offs: Overhead, Privacy, and Scale
Deep inspection is not free. Introducing an inline proxy added measurable but generally acceptable latency to network-heavy stages, more noticeable during large package resolutions than compute-bound compilation. Teams with latency-sensitive builds needed to stage rollouts and baseline metrics to avoid conflating expected overhead with regressions elsewhere.
Privacy and compliance raised legitimate questions. Because BAF inspects payloads before encryption, organizations had to define data handling rules and audit trails, especially in regulated sectors. The product supplied logging controls and reporting hooks, yet responsibility for policy scoping remained with operators. Handling ephemeral environments at scale also challenged teams that rotate runners aggressively; integration maturity mitigated this, but cross-CI parity beyond GitHub Actions remained a gap to watch.
Competitive Landscape: Why BAF and Not Alternatives
SAST and SCA competitors scan code and manifests exceptionally well, but they do not see live traffic. CNAPP tools monitor cloud runtime, typically after artifacts are deployed. Network egress filters and service meshes can restrict destinations, yet they rarely inspect build payloads pre-encryption and cannot attribute dependency truth to a specific job. BAF’s unique angle was blending active prevention of exfiltration with runtime-derived provenance inside CI.
Some vendors tout post-build forensics or SBOM enrichment as a substitute. Those help with incident response and compliance but do not block the heist while it unfolds. BAF’s competitive strength lay in executing at the moment of risk, paired with enough ecosystem intelligence to cut noise rather than add it. The main counterpoint was platform breadth—teams outside GitHub Actions may need patience for first-class support.
Use in Practice: Sectors, Scenarios, and Outcomes
SaaS and fintech adopters valued strict egress control that did not break builds; warn-first policies mapped traffic patterns, then deny rules closed off shadow destinations. Healthcare and embedded software groups leaned on TruSBOM to validate what actually shipped when caches and cross-ecosystem pulls complicated provenance, improving change control and audit narratives.
Concrete wins tended to cluster around two moments: blocking encoded exfiltration hidden in routine dependency fetches, and proving true package versions when mirrors or caches muddied records. In both, BAF converted ambiguous risk into actionable decisions—tighten allow-lists without guesswork, approve exceptions with confidence, and maintain throughput by targeting enforcement where it counted.
Verdict: Runtime Control Became the Missing Layer
Taken together, v1.1.38 showed that stopping credential theft at build time and documenting real dependency behavior could be delivered without derailing developers. The encoded secret interception closed a modern, high-impact vector; the TruSBOM clarified provenance disputes that slowed remediation; the hardened GitHub Actions integration reduced rollout friction. Limitations persisted—overhead must be measured, privacy scoped, cross-CI parity expanded—but the core thesis held up under scrutiny.
For security leaders, the actionable path was to pilot BAF in warn mode on representative pipelines, instrument latency baselines, and use runtime graphs to reconcile SBOM discrepancies before turning on denies. For platform teams, the choice was less “add one more scanner” and more “enforce the one layer that actually sees the act.” As supply-chain attacks continued to hide in trusted paths and encrypted channels, a build-time firewall read as a necessary complement, not a luxury, and this release positioned InvisiRisk as a credible standard-bearer for that model.