The digital landscape has long wrestled with a fundamental trade-off where the utility of shared data inevitably demands the surrender of absolute privacy. For decades, the “transparency paradox” meant that to process information, one had to expose it, leaving sensitive financial and personal details vulnerable the moment they were put to work. Fully Homomorphic Encryption (FHE) has finally broken this deadlock, evolving from a dense mathematical theory into a high-performance protocol stack that allows computers to calculate results using encrypted data without ever seeing the underlying information.
The Evolution and Principles: Breaking the Transparency Paradox
FHE represents the “holy grail” of cryptography because it ensures that the result of an operation performed on ciphertext, once decrypted, is identical to the result of that same operation performed on plaintext. Unlike traditional encryption that protects data only at rest or in transit, FHE protects data during its most vulnerable state: while it is being processed. This shift effectively creates a privacy layer for the modern web that mirrors the security transition the internet underwent when it moved from vulnerable HTTP to the encrypted standards of HTTPS.
This technological leap is not merely about hiding numbers; it is about enabling a new form of “blind” computation. In a decentralized ecosystem, this means a smart contract can determine if a user has sufficient funds for a transaction or calculate a credit score without the network ever knowing the user’s actual balance or identity. By decoupling the ability to compute from the ability to see, FHE provides a foundation for trustless systems that do not require the sacrifice of personal or institutional secrets.
Core Components: Bridging Theory and Practical Development
Accessible Development Frameworks: Simplifying Complex Math
The transition of FHE into the mainstream has been accelerated by the arrival of specialized Software Development Kits (SDKs) that hide the terrifying complexity of lattice-based cryptography. Industry leaders like Zama have introduced toolkits that utilize familiar abstractions, such as ERC-20-style interfaces, allowing developers to write confidential logic using the same mental models they use for standard applications. These frameworks integrate seamlessly with popular libraries like TypeScript and React, meaning a developer does not need a doctorate to build a privacy-preserving app.
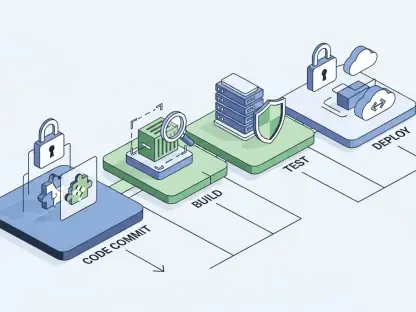
Delegated Decryption: The Path to Programmable Auditability
A critical innovation within the modern FHE stack is the concept of delegated decryption, which solves the friction between total anonymity and legal accountability. Absolute privacy often hinders institutional adoption because it bypasses regulatory oversight; however, FHE now allows for “programmable auditability.” This mechanism enables specific entities, such as compliance officers, to be granted limited, conditional permissions to decrypt specific data points. This ensures that while the public cannot see the data, the system remains compliant with global financial standards.
Current Innovations: The Rise of Standardized Confidentiality
The industry is currently moving toward a unified approach to private assets, moving away from the fragmented “privacy pools” of the past. The introduction of official confidential token wrappers, such as ERC-7984, allows major assets like USDC and WETH to be “shielded” within a standardized registry. This prevent liquidity from being split across different privacy protocols, ensuring that a private dollar remains as fungible and liquid as its public counterpart while benefiting from the full protection of homomorphic encryption.
Moreover, the integration of AI-native documentation and automated state query hooks has lowered the barrier for entry even further. Instead of manually managing complex encryption keys, developers can now use pre-built hooks that handle the heavy lifting of state management. This shift suggests that the industry is no longer just focused on making FHE work, but on making it work at scale, prioritizing a developer-centric landscape that encourages rapid experimentation across various blockchain environments.
Real-World Applications: From DeFi to Private Governance
Confidential Decentralized Finance: A New Financial Standard
FHE is already being utilized to build a private decentralized financial infrastructure that rivals the privacy of traditional banking while maintaining the transparency of the blockchain. Users can now “shield” their assets across major networks like Solana and BNB Smart Chain, performing trades and managing portfolios without broadcasting their strategies to the entire world. This capability is vital for preventing front-running and protecting the competitive advantages of institutional traders who require discretion.
Private Governance: Secure Multi-Chain Interactions
Beyond simple transfers, FHE enables sophisticated multi-chain bridging and private governance. By using Key Management System (KMS) nodes and staking models, networks can securely process private data in a distributed manner. This allows for autonomous agentic payments and private yield generation, where smart contracts execute financial logic based on encrypted triggers. Such a system ensures that sensitive trade secrets and individual user balances remain hidden even as the contract executes its programmed functions.
Challenges and Hurdles: The Performance Tax and Regulation
Despite the rapid progress, FHE still faces a significant “performance tax” due to the intense computational overhead required to process encrypted bits. Calculating on ciphertext is inherently slower than processing plaintext, which can limit the throughput of high-frequency applications. While hardware acceleration and better algorithms are narrowing this gap, the energy and time costs remain higher than traditional methods, posing a challenge for mass-market adoption in speed-sensitive sectors.
Furthermore, the global regulatory environment remains cautious about technologies that offer high levels of untraceability. Navigating these legal waters requires constant refinement of the auditability features mentioned earlier. Developers must strike a delicate balance between providing ironclad privacy for the average user and ensuring that the technology cannot be easily co-opted for illicit activities, a task that demands ongoing collaboration between cryptographers and policy makers.
Future Outlook: Moving Toward a Privacy-by-Default Internet
The trajectory of FHE suggests a future where encryption is not an optional feature but a default state of the digital world. As hardware acceleration continues to evolve, the current performance limitations will likely diminish, making encrypted computations as seamless as the unencrypted versions. This evolution will likely lead to an internet architecture where data remains encrypted throughout its entire lifecycle—from creation to processing and storage—fundamentally changing how we interact with digital services.
In the coming years, we should expect FHE to integrate more deeply with artificial intelligence, allowing for “private learning” where models can be trained on sensitive medical or financial data without ever actually “seeing” the raw information. This synergy between AI and FHE could unlock vast amounts of siloed data for research and innovation, all while maintaining the highest standards of individual privacy and data sovereignty.
Final Assessment: A Foundational Shift in Digital Security
Fully Homomorphic Encryption successfully transitioned from a theoretical curiosity into a cornerstone of the next-generation digital economy. By providing a functional solution to the transparency paradox, it allowed for the creation of systems that are both public and private, transparent yet confidential. The introduction of accessible SDKs and robust staking ecosystems demonstrated that the technology was ready for institutional and consumer-grade applications, effectively bridging the gap between data utility and security.
The move toward standardized registries and programmable auditability signaled a mature approach to privacy that respected both user rights and regulatory frameworks. While technical hurdles regarding computational speed persisted, the path forward became clear through the lens of hardware optimization and standardized protocols. Ultimately, FHE set the stage for a new era of cybersecurity where data protection became an intrinsic property of the network itself, ensuring that the future of global finance and digital interaction remained secure by design.