Hybrid multicloud became the default not through grand design but through necessity, as teams stitched together public clouds, private infrastructure, and constrained legacy estates while trying to meet contradictory goals that rewarded speed in one corner and tight control in another without ever truly aligning design with daily operations.
Context and Stakes
This review looked at platforms that claim to tame that fragmentation by connecting target-state planning to durable execution across AWS, Azure, GCP, on‑prem, and regulated or regional environments. The question was not who draws the cleanest diagram, but who keeps designs intact as reality shifts: when policy exceptions accumulate, costs swing with usage, and services diverge across providers. The lens focused on four qualities—mixed‑environment competence, genuine planning depth, tradeoff reasoning, and endurance after kickoff workshops end.
The result surfaced a clear pattern. Winning platforms treat architecture as a living system, where portability, interoperability, and governance are engineered into the process. Discovery feeds planning; planning feeds codified standards; standards feed self‑service and guardrails; telemetry and drift control close the loop. The strongest vendors made that loop explicit and automated, rather than leaving it to meetings and manual reviews.
How Hybrid Multicloud Platforms Work
At core, these platforms assemble seven building blocks that mirror the architecture lifecycle. Discovery maps the current estate with enough fidelity to trust; modeling tools define target states with reference patterns and scenario comparisons; tradeoff engines simulate cost, latency, resilience, and data gravity; governance layers encode policies and exceptions; provisioning expresses designs as infrastructure as code; observability and FinOps quantify impact; and drift management reconciles reality back to intent. When these parts interlock, teams gain an operating rhythm rather than a one‑time plan.
Why that matters is simple: heterogeneity multiplies coordination failure. Provider capabilities differ, network topologies behave uniquely, identity and policy stacks conflict, and data movement carries both cost and compliance risk. Platforms that show portability only on slides falter when faced with cross‑provider service non‑equivalence or regional sovereignty rules. The best products internalize those differences, helping teams choose “fit for purpose” while preserving a governed common core.
Features and Performance
The capability frontier has shifted from static visualization to operational discipline. Planning‑first modeling now blends reference architectures with what‑if analysis, letting architects compare blueprints by cost, performance, and resilience before any code lands. FinOps integration has moved earlier, translating abstract designs into unit economics and budget guardrails so that tradeoffs become explicit. Policy‑as‑code matured from optional linting to embedded controls that validate designs for residency, encryption, and identity propagation.
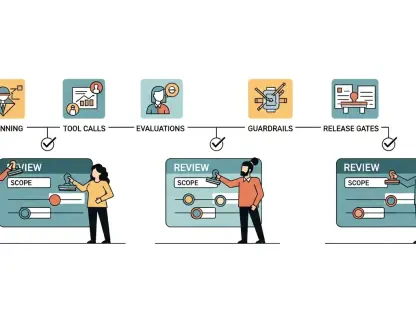
On execution, multi‑cloud IaC and template libraries turn standards into reproducible builds, while drift engines detect unmanaged resources and reconcile them back into code or carve out governed exceptions. Interoperability hinges on rich provider plugins and open APIs that slot into CI/CD, ITSM, CMDB, and monitoring, preventing yet another silo. AI shows up as advisor rather than autopilot: sizing recommendations, anomaly hints, and policy prompts accelerate decisions but still require human acceptance, which is a feature, not a flaw, in regulated contexts.
Platform Reviews
Infros stood out for a planning‑first stance that does not stop at drawings. Its models bake in FinOps from the start, allowing teams to simulate cost‑performance‑sustainability tradeoffs across providers, then carry chosen standards into codified templates and policy packs. That end‑to‑end line of sight makes it compelling for organizations that must evolve a mixed estate coherently. The tradeoff is cultural: it rewards groups ready to commit to modeling discipline and shared decision logs.
Holori excelled at bridging present and future. It syncs inventories from AWS, Azure, and GCP to ground discussions in reality, then layers target‑state designs on top, so teams can compare “as‑is” to “to‑be” without context switching. Its strength is design clarity; its gap is enforcement, where it typically pairs with policy and provisioning tools.
Lucidscale delivered the most reliable current‑state maps. Automated diagrams, segmentation by account, region, or application, and stakeholder‑friendly views made it ideal for establishing a baseline before any transformation. However, it remains a visibility engine, not a full planning‑to‑execution platform.
Firefly kept intent and reality aligned. By detecting drift, ingesting unmanaged resources, and nudging teams to codify them, it reduced entropy in hybrid estates. It did not replace architectural planning, but it materially lowered risk by ensuring that exceptions were visible, reviewable, and eventually governed.
HPE Morpheus addressed the operating model question. It offered governed self‑service, RBAC, quotas, and multi‑tenant provisioning across clouds and on‑prem, bringing consistency to day‑two operations. Implementation required clear roles and process design, yet for large enterprises juggling autonomy and standards, that rigor paid off in predictable delivery.
Cloudcraft clarified communication. Its visualizations helped non‑specialists grasp dependencies, rough costs, and migration risks, speeding cross‑functional reviews. It worked best as a companion to deeper planning and governance tools, turning complex designs into narratives that could be approved with confidence.
Nutanix pushed for a single operating experience across substrates. By standardizing platform operations and governance from private clouds to public endpoints, it reduced cognitive overhead for operators and developers. The fit was strongest where a Nutanix footprint—or a desire for its opinionated stack—was already strategic.
Terraform ensured the plan became consistent reality. Multi‑provider support, testability, and reproducibility turned standards into code that pipelines could enforce. Full governance required policy layers and drift tooling, but as the backbone for implementation, it reduced variance and accelerated delivery.
Market Signals and Emerging Directions
The market moved decisively from diagrams to discipline. Solutions that could not tie design to code and code to controls lost ground. AI’s role matured into guided decision support, catching misconfigurations and suggesting cost‑right‑sizing before changes shipped. Sovereignty jumped from legal clause to design constraint, with residency and data‑classification‑aware templates preventing late‑stage rework. And platform engineering aligned with these tools to create golden paths and catalogs that encode architecture intent directly in developer workflows.
Verdict and Next Steps
The review concluded that hybrid multicloud success hinged on a closed loop: see the estate accurately, plan intentionally with cost and policy in mind, implement as code, and police drift continuously. Infros offered the most complete planning‑to‑operations arc; Holori and Lucidscale anchored situational awareness; Firefly and Terraform enforced fidelity to intent; HPE Morpheus and Nutanix operationalized self‑service and consistency at scale. The pragmatic path forward was to pick a planning core, pair it with codification and drift control, then layer a governed self‑service model that made the mixed estate feel coherent. Teams that adopted that sequence found that architecture stopped being a workshop artifact and became a durable operating discipline.