Software moved faster than governance, faster than architecture, and faster than most teams could safely absorb, and that speed exposed a new class of failures where AI-generated code looked correct in isolation yet quietly broke security guarantees, drifted from service contracts, and collapsed under cross-repo complexity that unit tests never exercised. The pitch behind spec-driven development is simple but radical: stop treating specifications as stale documentation and start executing them as the gatekeepers of architectural truth, letting machines enforce the contracts that humans mean instead of hoping a checklist and a code review will catch issues after the fact.
At its best, Spec-Driven Development (SDD) converts intent into an enforceable artifact that both agents and pipelines read as law. This review examines how SDD evolved, what it looks like in practice, and where it actually changes engineering economics. The analysis also weighs costs and limits, compares SDD to adjacent methodologies, and interprets recent evidence on AI security, governance, and multi-repository coordination. The net question is direct: does SDD meaningfully alter outcomes for organizations leaning into AI-assisted delivery, or does it merely shift complexity from code to specification?
Foundations and Context: What SDD Is and Why It Emerged Now
SDD defines specifications as executable contracts that live in the build and determine whether code can advance. Unlike a PRD that a human interprets, an SDD spec is written for tools and agents first: constraints are machine-verifiable, verification steps are codified, and architectural rules fail the build on divergence. This flips the traditional flow. Instead of writing code and then checking if it fits the architecture, teams encode architecture and behavior upfront, and the pipeline becomes the enforcer.
The timing is not accidental. Three forces converged. First, AI code generation began operating at industrial scale, and so did its vulnerabilities. Multiple studies found high rates of security defects in AI-generated code, including BLOCKER and CRITICAL severities that slip past unit tests but bite hard in production. Second, compliance tightened. Regulations now expect traceable development processes where specifications act as evidence, not suggestions. Finally, distributed architectures grew more entangled, multiplying cross-service failure modes that cannot be tamed by local tests alone. In combination, these dynamics created a governance void that SDD explicitly fills.
Moreover, SDD aligns with the rise of autonomous and semi-autonomous agents. As teams delegate more to machines, ambiguity becomes operational risk, not just stylistic debt. Microservices sprawl compounds the problem: integrations fail not because a single function is wrong, but because shared contracts or assumptions drift invisibly. SDD’s proposition is to stabilize this surface with explicit, enforceable truth that resists non-determinism and institutional amnesia.
Architecture and Core Components of SDD
Executable Specifications and Validation Gates
SDD specifications are designed to be parsed and enforced. They encode acceptance criteria, constraints, and checks that CI/CD can evaluate; when the code diverges from the spec, the pipeline fails decisively. This moves correctness from “review found it” to “system prevented it,” reframing quality as a property of the release process rather than discretionary judgment. System-level checks catch misalignments that unit tests are not structurally able to observe, such as cross-service contract drift or performance guarantees under realistic traffic shapes.
This orientation distinguishes SDD from design docs and PRDs. Human-facing documents tolerate ambiguity because colleagues fill gaps with shared knowledge. Agents interpolate, too, but they do so mechanically, which often leads to superficially plausible yet architecturally invalid solutions. An SDD spec reverses the burden by making uncertainty explicit and encoding how to measure conformance. The net effect is reduced ambiguity for agents and less regression risk when code is regenerated.
Multi-Agent Roles: Coordinator, Implementors, and Verifier
SDD typically uses a separation-of-duties pattern. A Coordinator agent decomposes the work, maintains the living spec, and arbitrates trade-offs as context evolves. Implementor agents execute against sub-specs in parallel, operating in isolated worktrees to avoid collisions. A distinct Verifier agent evaluates outputs against explicit criteria, acting as an adversarial counterweight to optimistic implementors. This split is not academic; it deliberately reduces correlated failure by ensuring the entity producing code is not the final judge of its adequacy.
This structure also raises the specification bar. To allow a Verifier to succeed, the spec must define criteria with practical precision: concrete data shapes, idempotency guarantees, error semantics, latency bounds, and compatibility constraints. The feedback loop strengthens specs over time because verification gaps surface as pipeline failures rather than production incidents. In multi-team settings, the pattern keeps parallel workstreams safe by sequencing integration through enforceable checkpoints rather than ad hoc agreements.
Six Critical Elements of an SDD Spec
High-fidelity specs share six elements that constrain behavior and reduce ambiguity. Outcomes make success observable, focusing on what must be true when work is done, not just what code exists. In-scope and out-of-scope boundaries prevent agents from expanding tasks opportunistically, a common failure mode when “adjacent” functionality seems reasonable to add. Constraints and assumptions codify realities the code must respect—API rate limits, data residency, chosen cryptography, or performance budgets—so implementors do not invent alternatives.
Documented prior decisions prevent re-litigation and block agents from diverging because they lack institutional memory. Task breakdown slices work into units that can be parallelized and verified, turning monolithically ambiguous tickets into concrete contracts. Finally, verification criteria translate goals into checks—tests to pass, properties to uphold, edge cases to exercise—so the Verifier can act as a deterministic gate. Together, these elements shrink the space where non-determinism can cause drift.
Governance Patterns: Spec-First, Spec-Anchored, and Spec-as-Source
SDD appears in three governance modes. Spec-First leads with constraint-led generation: specs precede code, and the pipeline enforces them. This is the entry point for most teams and offers immediate guardrails around AI. Spec-Anchored tightens control by adding constitutional constraints, checkpoints, and auditable trails, making specifications part of governance, not just delivery. This pattern pairs well with regulated environments where traceability and duty segregation are required.
Spec-as-Source pushes furthest: specs become the literal source of truth for API-first domains. When OpenAPI or AsyncAPI drive generation, the spec defines the interface and the pipeline produces compliant artifacts, reducing drift between code and contract. The trade-off is governance overhead and a possible bias toward big upfront specs. Used selectively, Spec-as-Source can eliminate entire classes of integration failure; applied indiscriminately, it can slow iterative work and calcify flexibility.
Tooling and Execution Substrate
A growing toolchain supports SDD. GitHub Spec Kit offers scaffolding and orchestration for agent workflows, providing a repeatable path from business context to implementable tasks and constrained execution. Contract and API tools, including SwaggerHub/API Hub, Postman Spec Hub, Spectral, PactFlow, Specmatic, and TypeSpec, cover authoring, linting, contract testing, and executable enforcement. Each plays a different role, from standardizing schemas to gating deploys with can-i-deploy checks.
At enterprise scale, control planes like Intent add semantic dependency mapping across massive codebases. By constructing a graph over hundreds of thousands of files, these systems enable cross-repository governance that single-repo tools cannot match. The combination lets organizations encode policy once, see where it applies, and enforce it consistently despite architecture sprawl. Certifications for security and AI governance increase confidence that the control plane can withstand audits without adding parallel paperwork.
Comparative Positioning in the Engineering Landscape
SDD vs TDD, BDD, and Prompt-Driven “Vibe” Coding
SDD sits above unit- and scenario-level practices. Test-Driven Development verifies how functions behave; Behavior-Driven Development frames cross-functional scenarios in human-readable language. SDD incorporates such scenarios as executable gates but holds a higher line by enforcing architectural and contractual invariants across services. It does not replace TDD or BDD; it contextualizes them within system-level constraints that must hold no matter how individual units perform.
The contrast with prompt-driven “vibe” coding is starker. Studies on assistant-led development documented transient velocity gains accompanied by persistent code complexity increase and architectural drift. Without architectural constraints, generation amplifies local optima that look useful in isolation but harm long-term maintainability. SDD counters this by defining guardrails upfront. The result is less seductive in demos—constraint rarely dazzles—but it pays off when code regenerations do not reintroduce previously fixed defects.
Preventing Drift and Establishing a Single Source of Truth
The core promise of SDD is a single, authoritative artifact that governs change. Specs are versioned, enforced in CI, and treated as the source of architectural truth, not as a slide deck no one updates. By localizing truth in a living specification, teams reduce the frequency of defects that reappear during regeneration or refactoring because constraints were never encoded where machines could read them.
This approach is especially powerful in integration-heavy environments. Cross-service compatibility is guarded by contract tests and schema linting that run as gates, not as optional checks. Removed endpoints stay removed because the spec defines deprecations and checks for reintroduction. Over time, SDD reduces the entropy that typically accumulates across microservices by keeping evolution explicit, documented, and enforced at the boundary where non-deterministic generation meets deterministic governance.
Recent Developments, Evidence, and Industry Trends
Security Posture of AI-Generated Code
Security data on AI-generated code is unambiguous and sobering. Multiple independent analyses found significant rates of vulnerabilities, including high proportions of BLOCKER and CRITICAL issues in popular models’ outputs. Findings also cataloged dozens of CWEs recurrently triggered by generation. The crucial interpretation is not that AI is uniquely unsafe, but that non-deterministic synthesis without architectural guardrails predictably yields repeat defects in familiar families: injection risks, broken auth flows, insecure defaults, and concurrency hazards.
SDD mitigates this pattern by baking CWE-aligned constraints into specs and turning them into enforceable gates. For example, specs can require idempotency for payment endpoints, mandate parameterized queries, or forbid insecure cryptography choices; the pipeline can then detect and block regressions automatically. The significance for teams is pragmatic: instead of fighting the same class of bug repeatedly after it ships, SDD prevents it from shipping at all, converting recurring incident cost into up-front specification work.
Regulatory and Compliance Momentum
Regulatory frameworks now assign real cost to weak governance, pushing organizations toward spec-as-evidence practices. High-risk AI obligations demand explainability, traceability, and auditable development processes. SDD’s Spec-Anchored mode slots into this reality: specifications become primary records that demonstrate what was required, how it was verified, and who approved it. Build logs and gate results form an evidentiary trail, eliminating the scramble to reconstruct intent from pull requests after the fact.
This shift changes incentives. Teams that might have tolerated informal agreements now benefit from formalizing constraints in specs that auditors can parse and systems can enforce. The strategic upside is that compliance work piggybacks on the delivery pipeline rather than becoming a parallel bureaucracy. The trade-off is cultural: adopting SDD raises the specification literacy bar across product and engineering, which not every organization is ready to meet.
Enterprise-Scale Coordination and Cross-Repository Context
Modern systems rarely fit in one repository. Shared libraries, infra-as-code, and microservices create a web of dependencies that resists local reasoning. SDD scales when it can see across that web. Semantic dependency mapping addresses the blind spot by building a knowledge graph that ties specs to code, contracts, and operational artifacts across repositories. With that map, spec violations become discoverable even when the change lands far from the interface that first defined the rule.
The practical benefit is coordinated evolution. Organizations can deprecate an API, propagate the spec change through the graph, and block deploys that ignore the new contract. When combined with can-i-deploy gates and consumer-driven contracts, the approach turns distributed change into a managed process rather than a synchronized leap of faith.
Real-World Applications and Implementation Patterns
API-First Systems and Contract Enforcement
API-first environments are SDD’s natural habitat. OpenAPI and AsyncAPI specifications become executable contracts that drive scaffolding, enforce backward compatibility, and gate deploys on schema and behavior. Idempotency, pagination semantics, and error shapes can be encoded as checks; drift is caught at build time rather than through customer reports. Because many tools natively support these formats, adoption friction is low and enforcement is direct.
The notable distinction is that SDD treats the spec as the deploy gate rather than as a generator-only input. With Spectral linting, PactFlow can-i-deploy checks, and Specmatic executable contracts, teams ensure consumers remain compatible, providers do not silently break contracts, and negotiated deprecations actually retire old paths. This closes the loop between intention and enforcement, which is often missing in API governance when the spec lives only in docs.
Frontend Delivery with Design Context (Figma MCP)
Frontend teams apply SDD by importing design systems and tokens directly into specs. With a design MCP integration, the Coordinator can extract grid rules, component variants, and typography scales from Figma, then encode them as constraints. Implementors then build pages with the same tokenized system that designers used, and the Verifier checks responsive behavior and component choices against explicit criteria.
The payoff is fewer subtle divergences—no competing button variants, no mystery spacing values—and smoother handoffs. Designers can navigate the spec-bound structure and adjust tokens without reverse-engineering code. Parallel decomposition by page or component becomes safe because the spec aligns everyone to a shared vocabulary, turning subjective “looks off” feedback into measurable conformance.
Brownfield Modernization and Incremental Enforcement
Brownfield adoption changes the playbook. Instead of trying to spec the universe, teams reconstruct critical behavior from legacy systems, codify the change surface, and enforce incrementally through CI. Reverse engineering focuses on observable artifacts—UIs, binaries, data lineage—so the spec reflects what users rely on rather than undocumented quirks. Each bug fix or refactor becomes a chance to add a specification slice that reduces regression risk going forward.
This stepwise strategy recognizes that SDD does not erase complexity; it relocates it into specs that must be maintained like code. The win is that complexity becomes explicit. Over time, the accreted specs form a safety net around the system’s most valuable seams, allowing modernization to proceed without destabilizing integrations that the organization cannot afford to break.
Representative Toolchains and Integrations
Adopters commonly assemble a toolchain that mixes open-source scaffolding, API lifecycle platforms, and enterprise control planes. GitHub Spec Kit covers spec authoring and agent orchestration. SwaggerHub/API Hub and Postman Spec Hub manage API lifecycles and governance, while Spectral enforces lint rules with CI-friendly exit codes. PactFlow and Specmatic operationalize contract testing; TypeSpec fits teams standardizing on Microsoft ecosystems by generating OpenAPI from higher-level definitions.
Enterprises extend this with a control plane such as Intent to build a semantic graph across large estates. The graph powers impact analysis, cross-repo traceability, and governance certifications. The net effect is consistent enforcement from design through deploy, with an evidentiary trail that satisfies internal risk teams and external auditors.
Limitations, Risks, and Adoption Challenges
When to Write a Spec vs When to Skip
Not every change deserves a full spec. Heuristics help: write specs when work spans sessions or services, when the wrong interpretation is expensive to reverse, or when auditability is non-negotiable. Skip them for quick, low-risk edits where a single prompt yields reviewable output in minutes. The goal is to align overhead with risk; otherwise, the specification burden can outweigh the value of speed and discovery.
This balancing act is central to SDD’s credibility. Over-specification breeds frustration and slows learning in exploratory phases. Under-specification hands too much latitude to non-deterministic agents. Mature teams treat the spec as a lever: tighten for high-impact surfaces, loosen for experiments where iteration beats governance.
Overhead, Organizational Fit, and Anti-Patterns
SDD front-loads work. It asks teams to invest in precise articulation of outcomes and constraints, then to maintain those specs as living documents. Big-bang specs are a known anti-pattern; they calcify insight and suppress feedback. The healthier path is progressive elaboration—grow the spec near the change surface, keep it close to code, and prune aggressively when intent no longer applies.
Adoption also has a cultural dimension. Organizations unused to governance-led development need to reset expectations about autonomy and approval. Product partners must supply clarity earlier. Engineers must embrace spec authorship as part of building, not as paperwork. Without that buy-in, SDD can look like overhead rather than like risk reduction, and teams may bypass gates in the name of speed.
Tooling Gaps and Cross-Repository Realities
Today’s mainstream tools still assume specs cohabit with code in a single repo, while real architectures span many. Co-location works until shared dependencies or infra drift across boundaries undo local guarantees. Cross-repo context engines and consistent spec taxonomies are necessary to operationalize SDD at scale. Without them, teams accumulate islands of governance that fail to prevent regressions when integration paths shift.
Standardizing spec naming, discovery, and lifecycle metadata also matters. If tools cannot reliably find and interpret the relevant spec for a change, enforcement becomes brittle. Investment in a control plane or in platform-level conventions often determines whether SDD remains a pilot or becomes a foundational practice.
Best Practices and Implementation Playbooks
Authoring High-Fidelity, Executable Specs
Good specs surface ambiguity early. Authors record decisions, codify constraints with concrete values, and define verification steps a machine can run. They keep specifications near the change surface, using directories and repos that mirror ownership boundaries so stewardship is obvious. Living specs evolve with work; they are not end-state documents frozen after discovery.
Precision beats volume. Overloaded context hurts agents by diluting signal. Pairing concise, task-relevant specs with a persistent project context file gives implementors enough background without flooding them with the entire codebase. The craft is in isolating what matters for this task, then proving it matters through executable checks.
CI/CD Integration and Build Gates
SDD earns its keep in CI. Linting prevents stylistic and schema drift; contract tests validate compatibility; can-i-deploy checks gate releases on consumer expectations; and exit codes enforce consequences. Teams often roll out progressively: start with Spec-First gating on a bounded service, then add Spec-Anchored checkpoints and constitutional constraints as complexity grows.
Observability closes the loop. Gates must be explainable, with failure messages tied to spec clauses and remediation steps. Without clear signals, developers treat gates as inscrutable blockers. With clarity, gates become learning tools that improve specs and implementations with each failure.
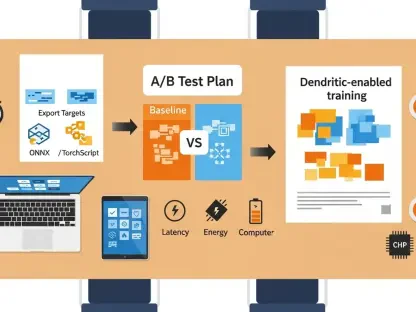
Model Selection and Cost Control for Multi-Agent Workflows
Multi-agent SDD changes model economics. The spec merits the strongest model because errors there propagate downstream and multiply rework. Implementation can use mid-tier models once constraints are solid. Verification benefits from fast, accurate models that cheaply run many checks. This tiering reduces cost without sacrificing quality where it matters most.
Managing non-determinism is equally important. Smaller, well-scoped tasks limit variance. Stable prompts, deterministic toolchains, and idempotent verification reduce correction loops. The measure of success is steady throughput with few surprises, not maximal novelty in generated code.
Measuring Outcomes and ROI
Organizations judge SDD by outcomes, not ceremony. Useful metrics include defect reintroduction rate after regeneration, security findings by severity, contract drift incidents, lead time for changes at critical interfaces, and rework cost. Auditable artifacts—spec versions, gate logs, approvals—serve both engineering health and compliance reporting.
Interpreting these metrics matters. A temporary increase in failures may signal that gates finally surfaced latent issues. A drop in post-deploy incidents with a modest increase in pre-merge failures often indicates healthier governance. The point is to align measurement with the risks SDD is designed to manage, then iterate on gates and specs accordingly.
Outlook and Future Directions
From Contracts to Constitutions
The next step for SDD is constitutional governance: embedding security controls, CWE mappings, and operational policies directly into specs and enforcing them at runtime and build time. Agents will operate within policy-aware sandboxes that prevent classes of unsafe actions by default. Architecture constraints will shift from advice to self-healing rules, correcting or blocking changes that violate performance budgets, data boundaries, or resilience patterns.
This evolution tightens the loop between design, implementation, and operations. With constitutions in place, teams can delegate more autonomy to agents without conceding control over non-negotiables. The likely outcome is fewer catastrophic surprises and more predictable iteration at scale.
Standardization and Interoperability
SDD benefits from converging formats and metadata. Cross-tool spec standards and lifecycle descriptors will allow linting, testing, and orchestration tools to interoperate without bespoke glue. Expanded MCP integrations will bring design, data contracts, and infra-as-code into the same governance surface, making specifications the nexus where disciplines meet.
Interoperability also reduces vendor lock-in. When specs travel cleanly, organizations can swap tools without rebuilding their governance model. That portability makes SDD a safer long-term bet for platforms choosing where to invest.
Safer Autonomy and Human-in-the-Loop
Verifier-first patterns, staged rollouts, and explainable gates point to safer autonomy. Human approval will remain critical at high-risk boundaries, but the surface will narrow as specs absorb routine checks. The emphasis will be on clarity: why a gate failed, which rule applied, and what remediation satisfies the constraint. This transparency keeps trust high even as agents take on more of the mechanical work.
Over time, human effort will concentrate on defining constraints and negotiating trade-offs that specs can encode. The work shifts from fixing the same bug repeatedly to designing the rule that prevents it from recurring.
Conclusion and Key Takeaways
SDD turned specifications from passive prose into active governance that shaped how AI-assisted systems were built, integrated, and audited. The distinctive value lay in enforcing intent at the pipeline boundary, where non-deterministic generation met deterministic checks. Compared with TDD and BDD, SDD addressed a higher stratum—system contracts, cross-service truth, and compliance evidence—while still harmonizing with those practices below.
The review found that SDD rewarded teams that matched overhead to risk, invested in high-fidelity specs, and deployed gates with clear signals. It penalized big-bang specs, shallow verification, and toolchains that stopped at single-repo visibility. Tool maturity improved the picture: API contract tooling and enterprise control planes made enforcement practical across complex estates, and CWE-aligned gates changed security from reactive patching to proactive prevention.
The verdict favored pragmatic adoption. Organizations gained most by starting Spec-First on a bounded service with contract gates, then expanding to Spec-Anchored governance where compliance and cross-repo change demanded it. API-first domains and frontend teams with design tokens saw outsized benefit from executable specs; brownfield modernization advanced when enforcement was incremental and anchored to the change surface. Looking ahead, constitutional specs, stronger interoperability, and verifier-led autonomy pointed toward systems that encoded policy as code and adapted safely under continual regeneration.